ARCHIVED STORY
Go Go Gadget Alerts! FireEye Helix utilizes data from Amazon Inspector for Investigations
By Christopher Unick · November 29, 2021
"Dr. Claw and M.A.D. Cat have started their cyber attack against Metro City. The security analysts in the Metro City SOC get a series of alerts that something is happening, but their systems are not integrated and they are spending hours just trying to collect data. By the time the analysts understand that an attack is occurring - Dr. Claw and his cat have Metro City held hostage. If the Metro City SOC was using Helix and Amazon Inspector, they could have called Inspector Gadget in to foil the attack."
Companies have hundreds of security tools, business applications and other data sources that can give them clues a security incident is occurring. Security analysts often feel overwhelmed with all the integrations they need in place just to gain visibility into their ecosystem and all the tools and gadgets they need to leverage just to get their job done. Organizations do not want to spend precious hours finding this information and trying to make sense of it, they want to be able to respond to an event or alert instantly with enough context to understand the threat. You shouldn’t have to be Inspector Gadget to connect all of telemetry for your security landscape. FireEye and AWS have taken the detective work out of your day job, by combining FireEye Helix and Amazon Inspector.

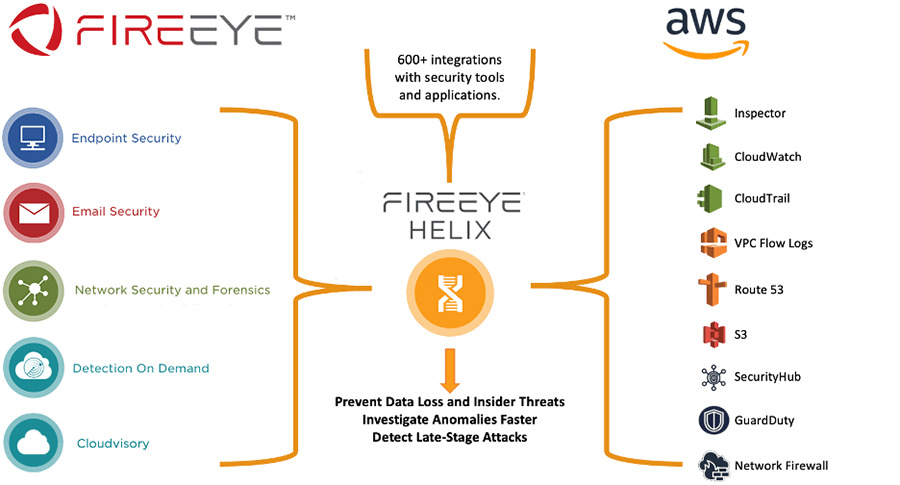
To protect against advanced threats, organizations need to integrate their security tools and apply the right expertise and processes. FireEye Helix, an AWS built SaaS security operations platform, utilizes Amazon Inspector findings to provide vulnerability and risk context for detection, visibility, and threat hunting activities. FireEye Helix integrates Amazon Inspector EC2 and ECR vulnerability data from your AWS infrastructure and correlates this information with data from over 650 different security and business applications. The Amazon Inspector Risk Score is then combined with Helix’s behavior analytics that can show when a compromised user leverages vulnerable infrastructure, possibly for insider threats, lateral movement, or other suspicious activity. This allows you to prioritize vulnerabilities to rapidly move from alert to fix. Imagine if Inspector Gadget had the right gadget specifically designed to stop Dr. Claw’s evil plans, it wouldn’t make for very compelling TV but Metro City would be a whole lot safer.
Amazon Inspector Overview
Amazon Inspector is an automated vulnerability management service that helps improve the security and compliance of workloads deployed on AWS. Amazon Inspector automatically assesses workloads for exposure, vulnerabilities, and deviations from best practices. After performing an assessment, Amazon Inspector produces a detailed list of security findings prioritized by level of severity. These findings can be reviewed directly or as part of detailed assessment reports which are available via the Amazon Inspector console or API.
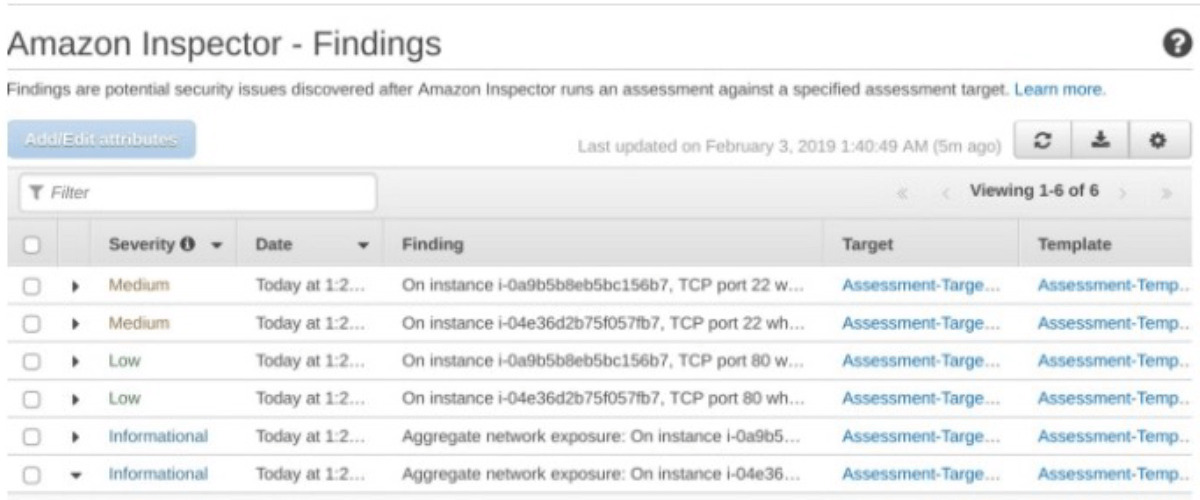
An Inspector risk score is created for each finding by correlating Common Vulnerabilities and Exposures (CVE) information with factors such as network access and exploitability. This score is used to prioritize the most critical vulnerabilities to help increase remediation response efficiency. All findings are aggregated in a newly designed Inspector console and pushed to AWS Security Hub and Amazon EventBridge to automate workflows. Vulnerabilities found in container images are sent to Amazon ECR for resource owners to view and remediate. With Inspector, even small security teams and developers can ensure infrastructure workload security and compliance across your AWS workloads.
How this Helps Our Mutual Customers
FireEye Helix eliminates all manual work for customers by instantly feeding key telemetry and findings from Amazon Inspector, along with Cloudwatch, VPC Flow logs, Network Firewall, CloudTrail, GuardDuty, Security Hub, S3 and Route 53. Amazon Inspector findings are another critical piece of information that can help reduce dwell time, the time it takes to discover a threat is happening. When Amazon Inspector risk scores are combined with FireEye Helix alerts and behavioral analysis, they help security teams perform investigations faster and reduce the time to resolve security issues. FireEye Helix is the tool that Inspector Gadget’s niece Penny would use to help solve her uncle’s problems, allowing her and loyal dog Brian to save the day, time and again.
Real Life Use Case
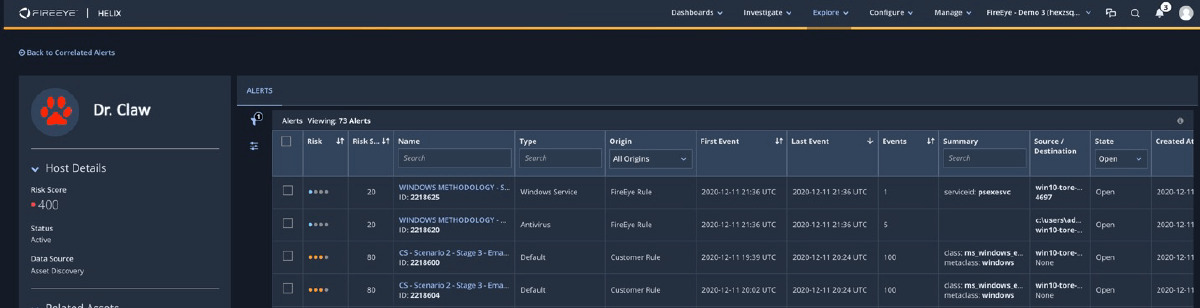
Threats can come from a multitude of vectors and the most common one can be from compromised credentials. A compromised account (Chief Quimby’s) can give attackers like Dr. Claw access to infrastructure or sensitive data that they can then use maliciously. With our combined integration, you can correlate a user's abnormal behavior across your holistic infrastructure with Amazon Inspector findings. This can help teams quickly prioritize the severity of an alert based on the changes in your AWS infrastructure (i.e., opening ports for network access to EC2).
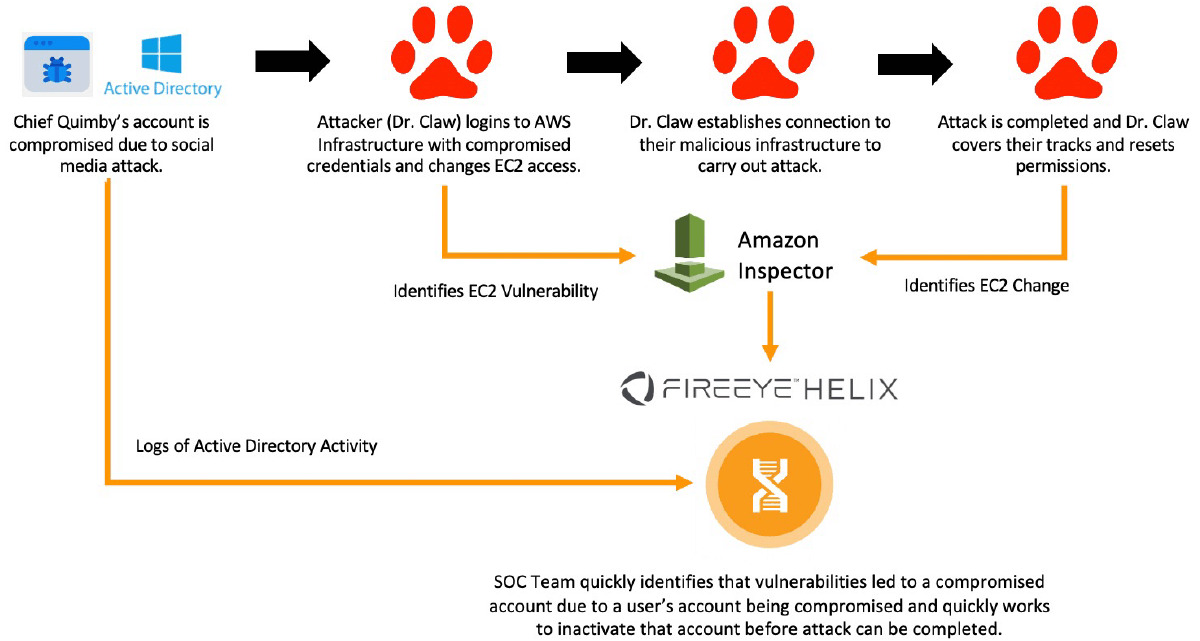
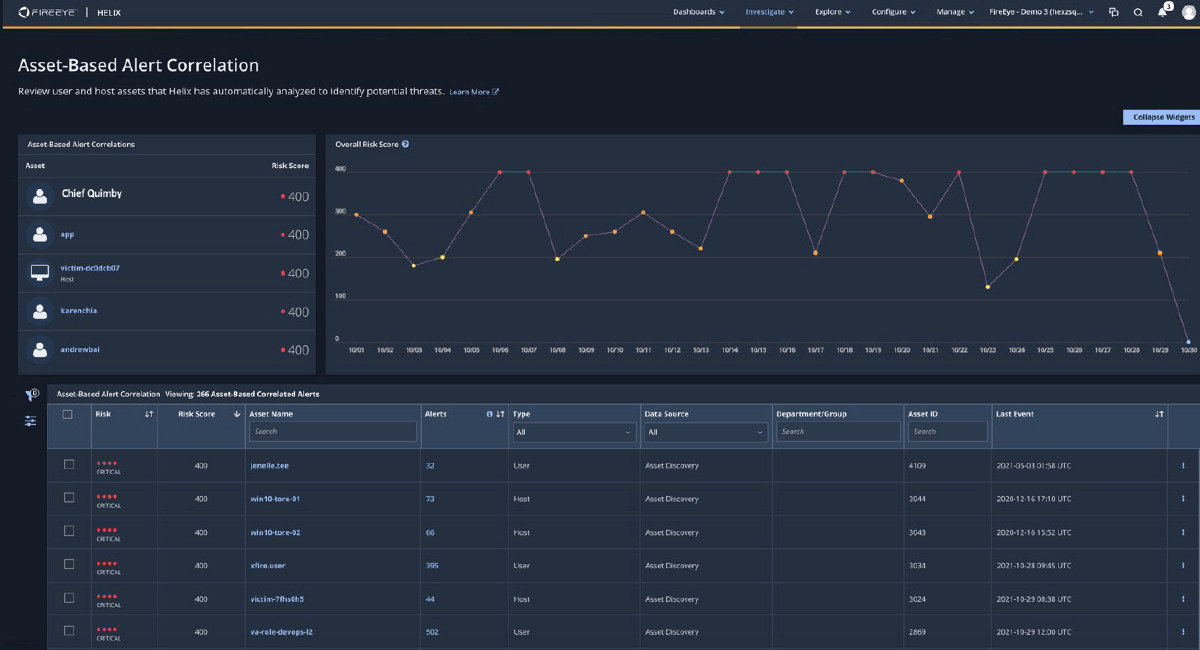
This will allow security teams to quickly focus on this risky user and be able to take action to remediate that account. FireEye Helix will show those users and assets that are at risk and allow you to drill down to understand all of the combined alerts you can take action on.
Even Inspector Gadget would say “Wowsers!” at the speed and efficiency used between Amazon Inspector and FireEye to allow customers to respond to security issues. Please reach out to aws_info@FireEye.com to learn more and to start a free trial of FireEye Helix today!
Additional Resources
RECENT NEWS
-
Jun 17, 2025
Trellix Accelerates Organizational Cyber Resilience with Deepened AWS Integrations
-
Jun 10, 2025
Trellix Finds Threat Intelligence Gap Calls for Proactive Cybersecurity Strategy Implementation
-
May 12, 2025
CRN Recognizes Trellix Partner Program with 2025 Women of the Channel List
-
Apr 29, 2025
Trellix Details Surge in Cyber Activity Targeting United States, Telecom
-
Apr 29, 2025
Trellix Advances Intelligent Data Security to Combat Insider Threats and Enable Compliance
RECENT STORIES
Latest from our newsroom
Get the latest
Stay up to date with the latest cybersecurity trends, best practices, security vulnerabilities, and so much more.
Zero spam. Unsubscribe at any time.